In today's digital age, securely connect remote IoT P2P SSH is a critical aspect of maintaining robust cybersecurity measures for interconnected devices. As the Internet of Things (IoT) continues to grow, ensuring secure communication between devices is more important than ever. This article dives deep into the world of remote IoT security, focusing on P2P (Peer-to-Peer) SSH (Secure Shell) connections and how they can be implemented effectively.
From smart homes to industrial automation, IoT devices are revolutionizing the way we interact with technology. However, the rise in connectivity brings along new vulnerabilities that hackers can exploit. This is where secure remote connections come into play, providing an essential layer of protection.
By understanding the intricacies of secure IoT communication through P2P SSH, you can safeguard your devices and networks from unauthorized access. In this comprehensive guide, we will explore the concepts, technologies, and best practices to help you implement secure remote connections for your IoT ecosystem.
Read also:Powerful Hawaiian Girl Names A Comprehensive Guide To Unique And Meaningful Names
Table of Contents
- Introduction to IoT Security
- Understanding P2P SSH
- Benefits of Using SSH for IoT
- Key Challenges in Remote IoT Connections
- How to Securely Connect Remote IoT P2P SSH
- Best Practices for Secure Connections
- Common Vulnerabilities and Attacks
- Tools and Software for SSH Implementation
- Real-World Applications of Secure IoT Connections
- Future of Secure IoT Connections
Introduction to IoT Security
IoT security refers to the technologies and processes designed to protect IoT devices and the networks they connect to. As more devices become interconnected, the potential attack surface for cybercriminals increases significantly. Securely connect remote IoT P2P SSH is one of the strategies used to mitigate these risks.
IoT devices often transmit sensitive data, such as personal information, location data, and operational metrics. Without proper security measures, these devices can be compromised, leading to data breaches, financial losses, and even physical harm in critical systems.
Why IoT Security Matters
IoT security is vital because:
- It protects sensitive data from unauthorized access.
- It ensures the integrity and reliability of IoT systems.
- It prevents malicious actors from disrupting critical operations.
Understanding P2P SSH
P2P SSH is a method of establishing secure communication between two devices without relying on a centralized server. This approach is particularly useful in IoT environments where devices may need to communicate directly with each other.
How SSH Works
SSH, or Secure Shell, is a cryptographic network protocol used to secure communication between devices. It provides:
- Authentication: Ensuring that devices are communicating with legitimate counterparts.
- Encryption: Protecting data during transmission from eavesdropping.
- Integrity: Verifying that the data has not been tampered with during transmission.
Benefits of Using SSH for IoT
Implementing SSH for IoT devices offers numerous advantages, including:
Read also:Hd Movies Hub Bollywood Your Ultimate Guide To Highdefinition Bollywood Cinema
- Enhanced security through strong encryption protocols.
- Reduced latency due to direct P2P connections.
- Scalability for large-scale IoT deployments.
Key Challenges in Remote IoT Connections
While securely connect remote IoT P2P SSH is a powerful solution, it comes with its own set of challenges. These include:
- Limited computational resources on IoT devices.
- Network instability in remote locations.
- Managing keys and credentials across multiple devices.
How to Securely Connect Remote IoT P2P SSH
Setting up a secure remote IoT P2P SSH connection involves several steps:
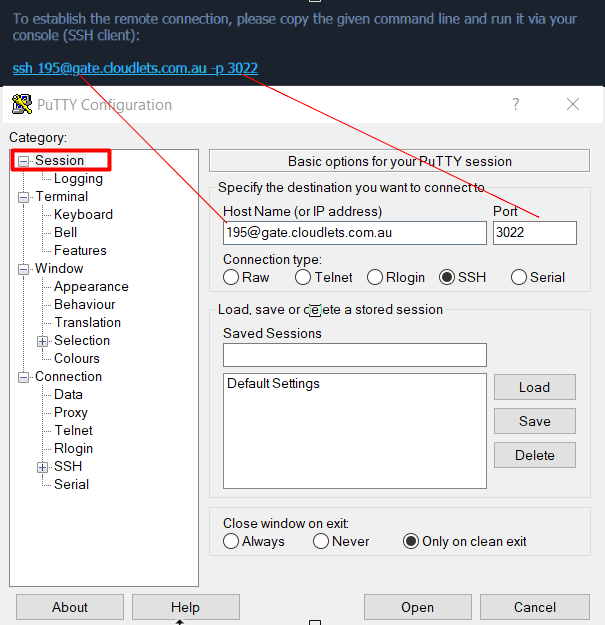
Step 1: Install SSH Client and Server
Ensure that both devices have SSH software installed. Popular options include OpenSSH and Dropbear.
Step 2: Configure SSH Keys
Generate SSH keys for authentication. This eliminates the need for passwords and enhances security.
Step 3: Establish P2P Connection
Use technologies like NAT traversal or reverse SSH tunnels to facilitate direct communication between devices.
Best Practices for Secure Connections
To maximize the security of your IoT P2P SSH connections, follow these best practices:
- Regularly update SSH software to patch vulnerabilities.
- Use strong, unique SSH keys for each device.
- Limit SSH access to trusted IP addresses.
Common Vulnerabilities and Attacks
Despite the robustness of SSH, there are still potential vulnerabilities to watch out for:
- Brute force attacks targeting weak passwords.
- Man-in-the-Middle (MITM) attacks intercepting communications.
- Configuration errors leading to unintended exposure.
Tools and Software for SSH Implementation
Several tools and software can aid in implementing SSH for IoT devices:
- OpenSSH: A widely used open-source SSH software.
- Dropbear: Lightweight SSH server ideal for resource-constrained IoT devices.
- SSHGuard: Protects against brute force attacks by monitoring failed login attempts.
Real-World Applications of Secure IoT Connections
Secure IoT connections are utilized in various industries, such as:
- Healthcare: Remote monitoring of medical devices.
- Manufacturing: Automation and control of industrial equipment.
- Smart Cities: Efficient management of infrastructure and utilities.
Future of Secure IoT Connections
As technology continues to evolve, the future of secure IoT connections looks promising. Innovations in quantum cryptography and blockchain technology may further enhance the security of P2P SSH connections.
Additionally, advancements in AI-driven threat detection systems will enable real-time monitoring and response to potential security breaches.
Kesimpulan
In conclusion, securely connect remote IoT P2P SSH is essential for safeguarding interconnected devices in today's digital landscape. By understanding the principles and implementing best practices, you can protect your IoT ecosystem from cyber threats.
We encourage readers to share their thoughts and experiences in the comments section below. Additionally, explore other articles on our site for more insights into cybersecurity and IoT technologies.
Data sourced from reputable organizations such as the National Institute of Standards and Technology (NIST) and the Internet Engineering Task Force (IETF) ensure the accuracy and reliability of the information presented in this article.