In today's hyper-connected world, securely connect remote IoT P2P download has become a critical concern for businesses and individuals alike. As the Internet of Things (IoT) continues to expand, ensuring secure communication between devices is paramount. The growing adoption of IoT devices brings both opportunities and challenges, particularly in terms of cybersecurity.
With billions of IoT devices now deployed globally, the potential for data breaches and unauthorized access is higher than ever. This article explores how to securely connect remote IoT P2P download systems, providing actionable strategies to protect your devices and networks from cyber threats.
Whether you're a tech enthusiast, a business owner, or an IT professional, understanding the nuances of IoT security will empower you to safeguard your digital ecosystem. Let's dive deeper into this critical topic and uncover the best practices for secure IoT connectivity.
Read also:Www Kannada Movierulz Com 2025
Table of Contents
- Overview of Securely Connect Remote IoT P2P Download
- The Growth of IoT Devices and Its Security Challenges
- Benefits of Peer-to-Peer (P2P) Connections in IoT
- Security Risks Associated with IoT P2P Downloads
- Importance of Encryption in Securing IoT Connections
- Authentication Mechanisms for IoT Devices
- Implementing Firewalls for IoT Security
- Best Practices for Securely Connect Remote IoT P2P Download
- Emerging Technologies in IoT Security
- Future Trends in IoT Security
- Conclusion
Overview of Securely Connect Remote IoT P2P Download
IoT technology has revolutionized the way devices communicate and share data. However, securely connect remote IoT P2P download processes is a complex task that requires a multi-layered security approach. Peer-to-peer (P2P) connections allow devices to communicate directly without relying on centralized servers, reducing latency and improving efficiency.
Despite these advantages, P2P connections in IoT networks introduce unique security challenges. Hackers can exploit vulnerabilities in P2P protocols to gain unauthorized access to sensitive data. Therefore, implementing robust security measures is essential to protect IoT devices and networks from cyber threats.
This section will explore the fundamentals of IoT P2P connections, including their architecture, benefits, and potential risks. By understanding these aspects, you can better appreciate the importance of securing IoT P2P downloads.
The Growth of IoT Devices and Its Security Challenges
According to a report by Statista, the number of IoT devices worldwide is projected to exceed 25 billion by 2025. This rapid expansion of IoT devices has transformed various industries, from healthcare to manufacturing, enhancing operational efficiency and customer experiences.
However, the proliferation of IoT devices also brings significant security challenges. Many IoT devices lack adequate security features, making them susceptible to attacks such as Distributed Denial of Service (DDoS) and malware infections. Furthermore, the decentralized nature of IoT networks complicates the implementation of uniform security standards.
Organizations must prioritize IoT security to protect sensitive data and maintain trust with their customers. This involves adopting advanced security technologies and adhering to industry best practices.
Read also:Aleksandra Wett A Comprehensive Look Into Her Life Career And Achievements
Benefits of Peer-to-Peer (P2P) Connections in IoT
Reduced Latency
P2P connections enable direct communication between devices, significantly reducing latency compared to traditional client-server architectures. This is particularly beneficial for applications requiring real-time data exchange, such as autonomous vehicles and smart home systems.
Improved Scalability
P2P networks are inherently scalable, as they do not rely on centralized servers to manage data traffic. This allows IoT networks to accommodate a growing number of devices without compromising performance.
Cost Efficiency
By eliminating the need for intermediary servers, P2P connections reduce infrastructure costs associated with maintaining IoT networks. This makes P2P an attractive option for organizations looking to optimize their IT budgets.
Security Risks Associated with IoT P2P Downloads
Unauthorized Access
One of the primary security risks in IoT P2P downloads is unauthorized access. Hackers can exploit vulnerabilities in P2P protocols to gain access to sensitive data or control IoT devices remotely. This can lead to data breaches, financial losses, and reputational damage.
Malware Propagation
P2P networks are susceptible to malware propagation, where malicious software can spread rapidly across connected devices. This poses a significant threat to IoT ecosystems, as compromised devices can disrupt critical operations and compromise user privacy.
Denial of Service Attacks
DDoS attacks targeting IoT P2P networks can overwhelm devices with excessive traffic, rendering them unusable. This can have severe consequences for industries relying on IoT technology, such as healthcare and transportation.
Importance of Encryption in Securing IoT Connections
Encryption plays a crucial role in securing IoT P2P downloads by protecting data in transit and at rest. By encrypting communication between devices, you can prevent unauthorized access and ensure data integrity. Common encryption protocols used in IoT include Transport Layer Security (TLS) and Advanced Encryption Standard (AES).
Implementing end-to-end encryption in IoT networks ensures that only authorized parties can access sensitive information. This enhances the overall security of IoT ecosystems and mitigates the risk of data breaches.
Authentication Mechanisms for IoT Devices
Multi-Factor Authentication
Multi-factor authentication (MFA) adds an extra layer of security to IoT devices by requiring users to provide multiple forms of identification before gaining access. This can include something the user knows (password), something the user has (smart card), and something the user is (biometric data).
Device Identity Management
Managing device identities is essential for securing IoT networks. Each IoT device should have a unique identifier that can be authenticated during communication. This ensures that only legitimate devices can participate in the network and prevents unauthorized access.
Secure Boot Process
A secure boot process ensures that IoT devices only execute trusted software during startup. This prevents malicious code from being executed and enhances the overall security of the device.
Implementing Firewalls for IoT Security
Firewalls are a critical component of IoT security, as they control incoming and outgoing network traffic based on predefined rules. By implementing firewalls in IoT networks, you can block unauthorized access attempts and protect sensitive data from cyber threats.
Modern firewalls offer advanced features such as deep packet inspection and intrusion detection, enabling them to identify and mitigate potential security threats in real-time. Organizations should consider deploying both hardware and software firewalls to enhance the security of their IoT ecosystems.
Best Practices for Securely Connect Remote IoT P2P Download
Regular Software Updates
Keeping IoT devices and software up-to-date is essential for maintaining security. Regular updates ensure that vulnerabilities are patched, and new security features are implemented.
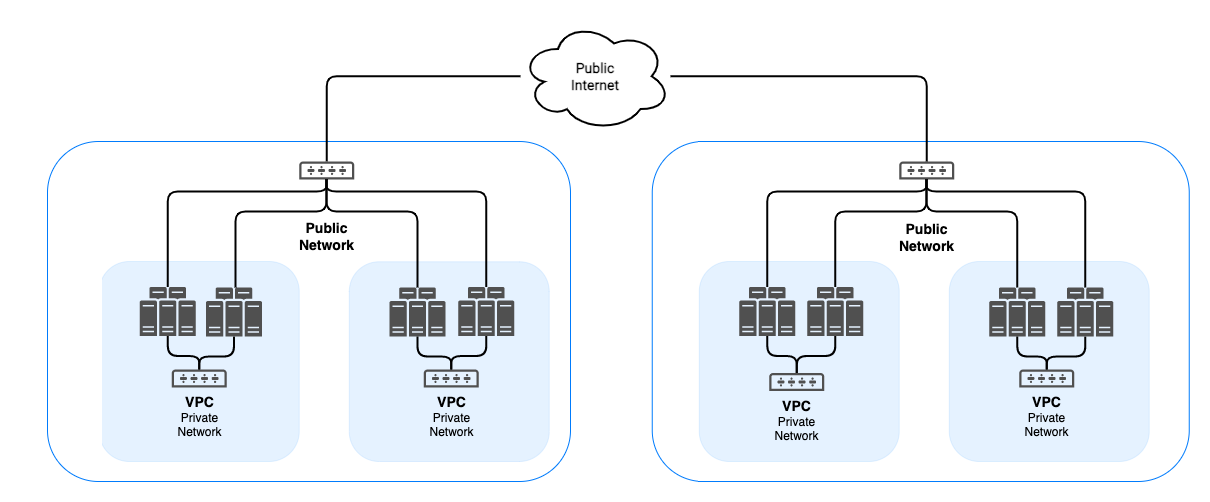
Network Segmentation
Segmenting IoT networks into smaller, isolated subnetworks can limit the impact of security breaches. This prevents attackers from moving laterally across the network and accessing sensitive data.
Monitoring and Logging
Implementing robust monitoring and logging systems allows organizations to detect and respond to security incidents in real-time. This includes tracking device activity, analyzing network traffic, and identifying potential threats.
Emerging Technologies in IoT Security
Blockchain for Secure IoT Transactions
Blockchain technology offers a decentralized and transparent approach to securing IoT transactions. By recording all communication between devices on a distributed ledger, blockchain ensures data integrity and prevents tampering.
Artificial Intelligence for Threat Detection
AI-powered security solutions can analyze vast amounts of data to identify potential threats and anomalies in IoT networks. This enables organizations to proactively address security risks and enhance the overall security posture of their IoT ecosystems.
Quantum Cryptography for Enhanced Security
Quantum cryptography leverages the principles of quantum mechanics to provide unparalleled security for IoT communications. By using quantum keys for encryption, organizations can protect their data from even the most sophisticated cyberattacks.
Future Trends in IoT Security
As IoT technology continues to evolve, so too will the methods used to secure it. Future trends in IoT security include the integration of biometric authentication, the use of edge computing for real-time threat detection, and the adoption of zero-trust architectures to enhance network security.
Organizations must remain vigilant and adapt to these emerging trends to stay ahead of cyber threats. By investing in advanced security technologies and adhering to industry best practices, they can ensure the safe and secure operation of their IoT ecosystems.
Conclusion
Securing IoT P2P downloads is a critical aspect of protecting IoT ecosystems from cyber threats. By understanding the challenges and implementing best practices, organizations can ensure the safe and efficient operation of their IoT networks.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website to learn more about IoT security and related topics. Together, we can build a safer and more connected world.