Connecting remote IoT devices through a secure peer-to-peer (P2P) network without incurring costs is a growing need in today's tech-driven world. The rise of IoT devices has transformed industries and personal lives, but ensuring secure communication remains a critical challenge. This guide aims to provide you with actionable insights into how you can achieve this seamlessly.
As more devices become interconnected, the demand for secure, cost-effective solutions grows exponentially. Businesses and individuals alike are looking for ways to implement secure IoT P2P connections without breaking the bank. This article delves into the strategies, tools, and best practices to help you achieve just that.
Whether you're a tech enthusiast, an entrepreneur, or simply someone interested in securing your IoT devices, this guide will equip you with the knowledge and resources you need. Let's explore how you can securely connect remote IoT devices using P2P technology for free.
Read also:Natalie Kaye Clater Bikini A Comprehensive Exploration Of Style Confidence And Influence
Table of Contents
- Introduction to Secure IoT P2P Connections
- Understanding IoT and Its Challenges
- What is Peer-to-Peer (P2P) Networking?
- How to Securely Connect Remote IoT Devices
- Free Tools for Secure IoT P2P Connections
- Best Practices for Securing IoT P2P Connections
- Privacy Considerations in IoT P2P Networks
- Cost-Effective Solutions for IoT Security
- Future Trends in IoT Security
- Conclusion and Call to Action
Introduction to Secure IoT P2P Connections
With the rapid expansion of the Internet of Things (IoT), connecting devices securely and efficiently has become paramount. IoT devices, ranging from smart home appliances to industrial machinery, rely on robust networks to function optimally. However, ensuring these connections are secure while keeping costs low is a challenge that many face.
Peer-to-peer (P2P) networking offers a promising solution for securely connecting remote IoT devices. By eliminating the need for centralized servers, P2P networks reduce overhead costs and enhance security. This section explores the basics of secure IoT P2P connections and why they are crucial in today's digital landscape.
Understanding IoT and Its Challenges
What is IoT?
The Internet of Things (IoT) refers to the network of physical objects embedded with sensors, software, and connectivity to exchange data with other devices and systems over the internet. From wearable fitness trackers to autonomous vehicles, IoT devices are transforming industries and enhancing daily life.
Challenges in IoT Security
Despite its benefits, IoT comes with significant security challenges. Devices often lack robust encryption protocols, making them vulnerable to cyberattacks. Additionally, the sheer volume of connected devices increases the attack surface for malicious actors. Understanding these challenges is the first step toward securing your IoT ecosystem.
What is Peer-to-Peer (P2P) Networking?
Peer-to-Peer (P2P) networking is a decentralized communication model where devices communicate directly with each other without relying on a central server. This approach offers several advantages, including enhanced security, reduced latency, and lower operational costs. In the context of IoT, P2P networking provides a scalable and efficient solution for connecting remote devices.
How to Securely Connect Remote IoT Devices
Key Components of Secure IoT P2P Connections
To securely connect remote IoT devices using P2P technology, consider the following key components:
Read also:Azariah Cartagena The Rising Star In The Entertainment Industry
- Encryption: Implement strong encryption protocols to protect data in transit.
- Authentication: Ensure all devices are authenticated before allowing them to join the network.
- Firewall: Use firewalls to monitor and control incoming and outgoing network traffic.
- Regular Updates: Keep firmware and software up to date to patch vulnerabilities.
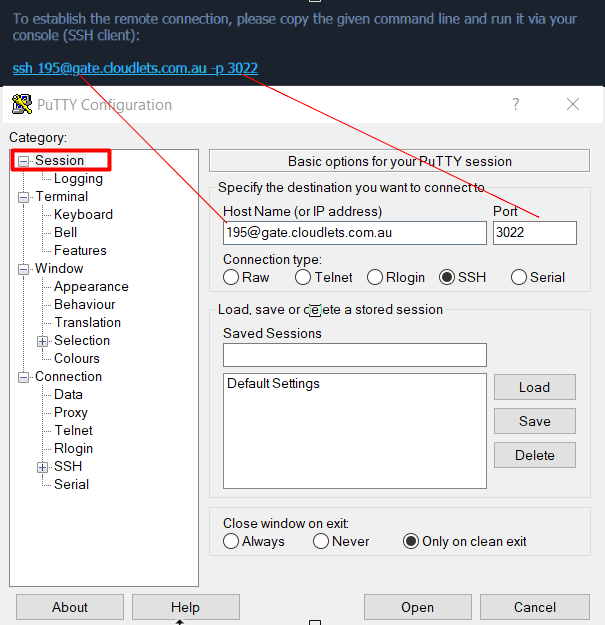
Steps to Implement Secure Connections
Here are the steps to implement secure IoT P2P connections:
- Identify the devices that need to be connected.
- Choose a suitable P2P protocol based on your requirements.
- Set up encryption and authentication mechanisms.
- Test the network for vulnerabilities and make necessary adjustments.
Free Tools for Secure IoT P2P Connections
Several free tools and platforms are available to help you establish secure IoT P2P connections. These tools often provide robust encryption, authentication, and monitoring capabilities. Below are some popular options:
- ZeroTier: A virtual network layer that allows you to create secure P2P connections.
- OpenVPN: An open-source VPN solution that can be configured for P2P use.
- Tailscale: A secure mesh networking tool that simplifies IoT device connections.
Best Practices for Securing IoT P2P Connections
Regular Security Audits
Conduct regular security audits to identify and address vulnerabilities in your IoT P2P network. This proactive approach ensures your devices remain secure against emerging threats.
Limit Device Access
Restrict access to your IoT network by only allowing authorized devices to connect. This minimizes the risk of unauthorized access and potential breaches.
Monitor Network Activity
Implement network monitoring tools to detect and respond to suspicious activities in real-time. This ensures prompt action can be taken to mitigate potential threats.
Privacy Considerations in IoT P2P Networks
Privacy is a critical concern in IoT P2P networks. Devices often collect and transmit sensitive data, making privacy a top priority. To protect user privacy, implement data anonymization techniques and comply with relevant data protection regulations such as GDPR and CCPA.
Cost-Effective Solutions for IoT Security
Securing IoT devices doesn't have to be expensive. By leveraging free and open-source tools, you can achieve robust security without incurring significant costs. Additionally, adopting a proactive security strategy reduces the likelihood of costly breaches and downtime.
Future Trends in IoT Security
The future of IoT security lies in advancements such as blockchain technology, AI-driven threat detection, and quantum encryption. These innovations promise to enhance the security and efficiency of IoT P2P networks. Staying informed about these trends will help you future-proof your IoT ecosystem.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices through P2P networks for free is achievable with the right tools and strategies. By understanding the challenges, implementing best practices, and leveraging cost-effective solutions, you can create a secure and efficient IoT network.
We encourage you to take action by exploring the tools and resources mentioned in this guide. Share your experiences and insights in the comments section below. Additionally, consider subscribing to our newsletter for the latest updates on IoT security trends and solutions.
References: