In today's interconnected world, securely connect remote IoT VPC has become a critical need for businesses and organizations aiming to protect their data and maintain seamless operations. With the rapid expansion of IoT devices, ensuring secure communication between remote networks and cloud environments is more important than ever. This guide dives deep into the strategies, tools, and best practices to securely connect remote IoT VPC, empowering you to safeguard your infrastructure effectively.
As more companies adopt IoT technologies, the challenge of maintaining robust cybersecurity measures has grown exponentially. The integration of IoT devices with cloud-based networks demands a secure virtual private cloud (VPC) setup to prevent unauthorized access and data breaches. This article will explore the steps and considerations required to achieve this goal.
Whether you're a network administrator, IT professional, or decision-maker in an organization, understanding how to securely connect remote IoT VPC is essential. By the end of this guide, you'll have a clear roadmap to enhance the security of your IoT infrastructure, ensuring both performance and protection.
Read also:Movierulz 2024 Download Telugu
Table of Contents
- Introduction
- Understanding VPC and Its Role in IoT
- IoT Security Challenges in Remote VPC
- Methods to Securely Connect Remote IoT VPC
- Best Practices for Securing IoT VPC
- Tools and Technologies for Enhanced Security
- Cloud Provider Support for IoT VPC Security
- Strategies for Data Protection in IoT VPC
- Importance of Network Monitoring for IoT VPC
- Future Trends in Secure IoT VPC Connections
- Conclusion
Understanding VPC and Its Role in IoT
A Virtual Private Cloud (VPC) plays a crucial role in securely connecting remote IoT devices. VPC provides an isolated environment within a public cloud where you can deploy your IoT applications and manage data securely. By leveraging VPC, organizations can control access to their resources, ensuring only authorized devices and users interact with the network.
Key Features of VPC in IoT
- Private IP addressing: Assign unique IP addresses to IoT devices within the VPC.
- Subnet management: Divide the network into smaller subnets for better control and security.
- Security groups: Define rules to allow or deny traffic to and from instances within the VPC.
- Network Access Control Lists (NACLs): Add an extra layer of security by filtering traffic at the subnet level.
Understanding these features is essential for setting up a secure IoT VPC environment that meets the demands of modern businesses.
IoT Security Challenges in Remote VPC
Securing remote IoT VPC environments presents several challenges that organizations must address:
- Limited device resources: Many IoT devices have limited processing power and memory, making it difficult to implement robust security measures.
- Diverse device types: The variety of IoT devices introduces complexity in managing security across different platforms and protocols.
- Data privacy concerns: Ensuring the privacy of sensitive data transmitted between IoT devices and VPC is a significant challenge.
Addressing these challenges requires a comprehensive approach that incorporates advanced security technologies and best practices.
Methods to Securely Connect Remote IoT VPC
Using IPsec for Secure Connections
IPsec (Internet Protocol Security) is a widely used protocol for establishing secure connections between remote IoT devices and VPC. It encrypts and authenticates data packets, ensuring confidentiality and integrity during transmission.
Implementing SSL/TLS
SSL/TLS protocols provide secure communication channels by encrypting data between IoT devices and VPC endpoints. This method is particularly useful for protecting sensitive information such as login credentials and financial data.
Read also:Movierulz Telugu
Both IPsec and SSL/TLS offer reliable solutions for securely connect remote IoT VPC, ensuring data remains protected from unauthorized access.
Best Practices for Securing IoT VPC
Adopting best practices is crucial for maintaining the security of your IoT VPC environment:
- Regularly update firmware and software to patch vulnerabilities.
- Implement strong authentication mechanisms, such as multi-factor authentication (MFA).
- Segment your network to isolate IoT devices from critical systems.
- Monitor network activity continuously to detect and respond to suspicious behavior.
By following these best practices, you can significantly enhance the security posture of your IoT VPC infrastructure.
Tools and Technologies for Enhanced Security
Firewalls and Intrusion Detection Systems
Deploying firewalls and intrusion detection systems (IDS) can help protect your IoT VPC from external threats. These tools monitor incoming and outgoing traffic, blocking malicious activities and alerting administrators to potential security breaches.
Encryption Technologies
Using advanced encryption technologies, such as AES (Advanced Encryption Standard), ensures data remains secure during transmission and storage. Encryption is a vital component in securely connect remote IoT VPC environments.
Incorporating these tools and technologies into your security strategy can provide an additional layer of protection for your IoT VPC.
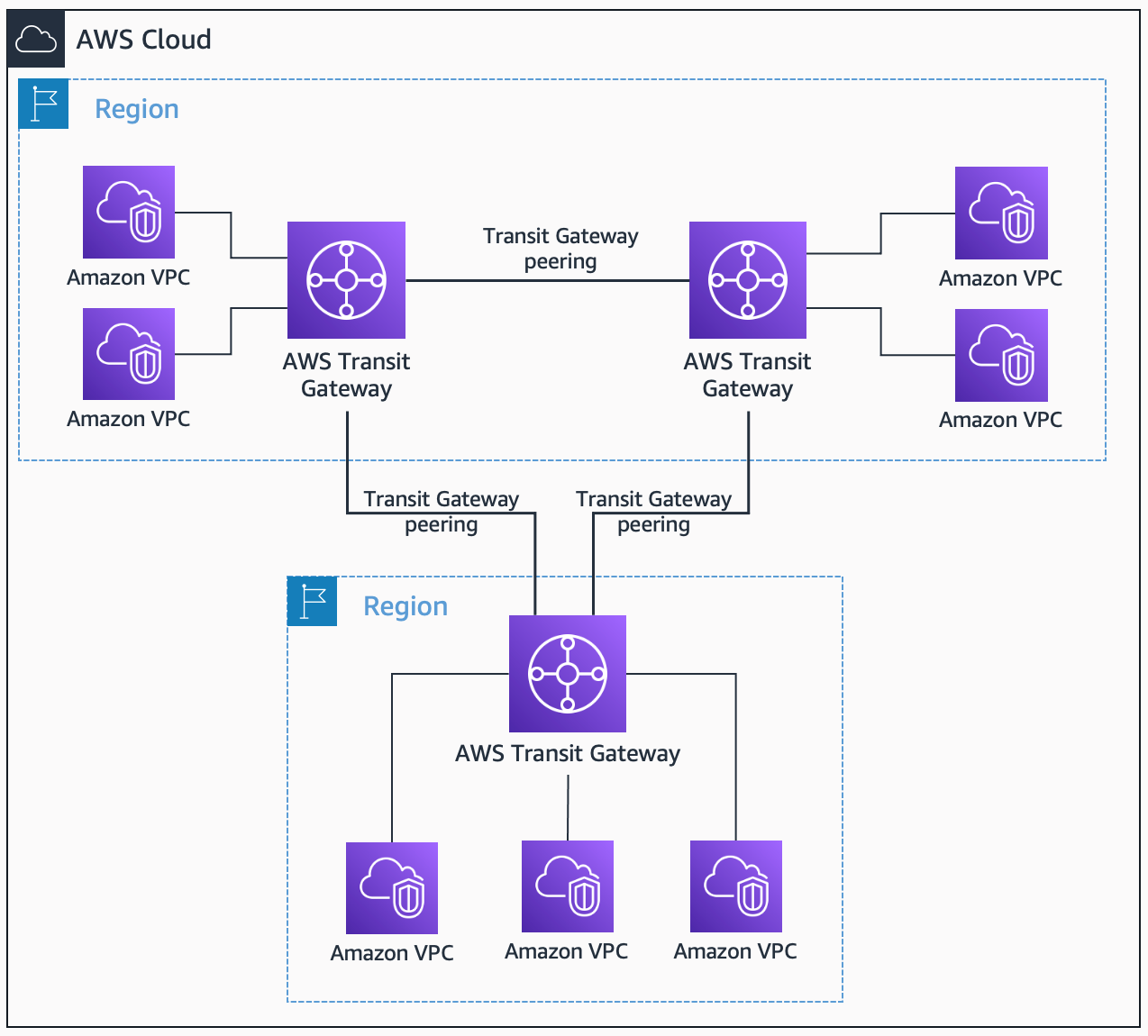
Cloud Provider Support for IoT VPC Security
Major cloud providers, such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP), offer built-in security features to help organizations securely connect remote IoT VPC. These features include:
- Managed firewalls and network access controls.
- Automated encryption and key management services.
- Comprehensive monitoring and logging capabilities.
Leveraging these cloud provider services can simplify the process of securing your IoT VPC environment while ensuring compliance with industry standards and regulations.
Strategies for Data Protection in IoT VPC
Data protection is a critical aspect of securely connect remote IoT VPC. Implementing the following strategies can help safeguard sensitive information:
- Data encryption: Encrypt data at rest and in transit to prevent unauthorized access.
- Data backup: Regularly back up data to ensure availability in case of a security incident.
- Data classification: Categorize data based on its sensitivity and apply appropriate protection measures.
By adopting these strategies, organizations can minimize the risk of data breaches and ensure compliance with data protection regulations.
Importance of Network Monitoring for IoT VPC
Continuous network monitoring is essential for detecting and responding to potential security threats in IoT VPC environments. Monitoring tools can help:
- Identify unusual traffic patterns and behaviors.
- Generate alerts for suspicious activities.
- Provide insights into network performance and security posture.
Investing in robust network monitoring solutions can enhance the overall security of your IoT VPC infrastructure, enabling proactive threat mitigation.
Future Trends in Secure IoT VPC Connections
The landscape of securely connect remote IoT VPC is evolving rapidly, with several emerging trends shaping the future of IoT security:
- Artificial intelligence (AI) and machine learning (ML): These technologies can enhance threat detection and response capabilities.
- Zero Trust Architecture: Adopting a zero-trust approach can improve security by verifying every connection attempt.
- Quantum encryption: As quantum computing advances, quantum encryption may become a viable option for securing IoT VPC environments.
Staying informed about these trends can help organizations prepare for the future of IoT security and maintain a competitive edge.
Conclusion
Securing remote IoT VPC environments is a complex but necessary task for organizations seeking to protect their data and maintain operational efficiency. By understanding the role of VPC in IoT, addressing security challenges, and implementing best practices, you can create a robust security framework for your IoT infrastructure.
We encourage you to take action by exploring the tools and technologies discussed in this guide and leveraging cloud provider support to enhance your IoT VPC security. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insights into cybersecurity and IoT.