As the Internet of Things (IoT) continues to expand, securely connecting remote IoT devices to Virtual Private Clouds (VPCs) on AWS has become a critical concern for businesses. In this digital age, ensuring robust security while maintaining seamless connectivity is paramount. This article will explore the strategies and best practices for securely connecting remote IoT devices to AWS VPC, offering actionable insights to safeguard your data and infrastructure.
Whether you're a developer, an IT professional, or a business owner, understanding how to implement secure connections for IoT devices in AWS VPC is essential. This guide will walk you through the process step by step, ensuring that your IoT ecosystem remains protected from potential threats.
With AWS offering a wide array of services to enhance security, this article will delve into practical methods and tools to help you achieve secure connectivity. By the end, you'll have the knowledge to set up and maintain a secure environment for your IoT devices.
Read also:Hdhub4uin Bollywood Your Ultimate Guide To Bollywood Movies And Entertainment
Table of Contents
- Introduction to AWS VPC
- IoT Security Challenges
- Secure Connection Methods
- Best Practices for IoT Security
- AWS Services for IoT Security
- Network Architecture Considerations
- Implementing VPC Peering
- Data Encryption Strategies
- Monitoring and Logging
- Conclusion and Next Steps
Introduction to AWS VPC
AWS Virtual Private Cloud (VPC) is a fundamental service that allows users to create an isolated section of the AWS Cloud where they can launch resources in a virtual network. This network is defined by the user and can be tailored to meet specific security and operational requirements. For organizations deploying IoT devices, securely connect remote IoT VPC on AWS is crucial for maintaining data integrity and privacy.
VPC provides several features that enhance security, such as private subnets, security groups, and network access control lists (ACLs). These features allow for fine-grained control over inbound and outbound traffic, ensuring that only authorized devices and services can communicate within the network. By leveraging these capabilities, businesses can create a secure environment for their IoT devices.
In addition to security features, VPC also offers scalability and flexibility, making it an ideal choice for IoT deployments. With the ability to integrate with other AWS services, VPC enables organizations to build robust and secure infrastructures for their IoT ecosystems.
IoT Security Challenges
Securing IoT devices presents unique challenges due to their diverse nature and widespread deployment. One of the primary concerns is the potential for unauthorized access, which can compromise sensitive data and disrupt operations. To securely connect remote IoT VPC on AWS, organizations must address these challenges head-on.
Key Challenges
- Device Authentication: Ensuring that only legitimate devices can access the network is crucial for preventing unauthorized access.
- Data Privacy: Protecting sensitive data transmitted between IoT devices and the cloud is essential for maintaining user trust.
- Network Vulnerabilities: IoT devices often operate on insecure networks, making them susceptible to attacks.
- Scalability: As the number of IoT devices grows, maintaining a secure and scalable infrastructure becomes increasingly challenging.
By understanding these challenges, organizations can implement strategies to enhance security and ensure the safe operation of their IoT devices.
Read also:Hdhub4u Hollywood Movies Your Ultimate Destination For Highquality Entertainment
Secure Connection Methods
To securely connect remote IoT VPC on AWS, it is essential to use proven methods that prioritize security and reliability. Below are some of the most effective techniques:
1. TLS Encryption
Transport Layer Security (TLS) is a widely used protocol for securing communications between devices. By encrypting data transmitted between IoT devices and AWS VPC, TLS ensures that sensitive information remains protected from interception.
2. Mutual Authentication
Mutual authentication involves verifying the identity of both the client and server, ensuring that only authorized devices can access the network. This method adds an extra layer of security, reducing the risk of unauthorized access.
3. Network Segmentation
Segmenting the network into smaller, isolated segments can limit the potential impact of a security breach. By restricting access to specific resources, network segmentation helps protect sensitive data and infrastructure.
Best Practices for IoT Security
Implementing best practices for IoT security is crucial for ensuring the safe operation of devices and maintaining data integrity. Below are some key practices to consider:
- Regular Updates: Keep firmware and software up to date to address known vulnerabilities and enhance security.
- Strong Passwords: Use complex passwords and implement multi-factor authentication (MFA) to protect against unauthorized access.
- Device Monitoring: Continuously monitor IoT devices for suspicious activity and take immediate action if any issues are detected.
- Access Control: Implement strict access controls to ensure that only authorized personnel can manage IoT devices and infrastructure.
By adhering to these best practices, organizations can significantly reduce the risk of security breaches and protect their IoT ecosystems.
AWS Services for IoT Security
AWS offers a variety of services designed to enhance IoT security and facilitate secure connectivity. Below are some of the most relevant services for securely connect remote IoT VPC on AWS:
1. AWS IoT Core
AWS IoT Core provides a managed cloud service that allows IoT devices to interact securely with cloud applications and other devices. It supports secure device authentication and communication, ensuring that data remains protected throughout the network.
2. AWS Shield
AWS Shield protects against Distributed Denial of Service (DDoS) attacks, which can disrupt IoT operations and compromise data security. By leveraging this service, organizations can maintain uninterrupted connectivity and protect their infrastructure from malicious attacks.
3. AWS WAF
AWS WAF (Web Application Firewall) helps protect web applications from common web exploits by filtering and monitoring HTTP and HTTPS traffic. This service can be used to safeguard IoT applications and ensure secure communication between devices and the cloud.
Network Architecture Considerations
Designing a secure network architecture is essential for ensuring the safe operation of IoT devices within AWS VPC. Below are some key considerations to keep in mind:
- Private Subnets: Use private subnets to isolate IoT devices from the public internet, reducing the risk of unauthorized access.
- Security Groups: Implement security groups to control inbound and outbound traffic, ensuring that only authorized devices can communicate within the network.
- Network ACLs: Use network access control lists (ACLs) to add an extra layer of security by defining rules for allowed and denied traffic.
By carefully designing the network architecture, organizations can create a secure environment for their IoT devices and protect sensitive data.
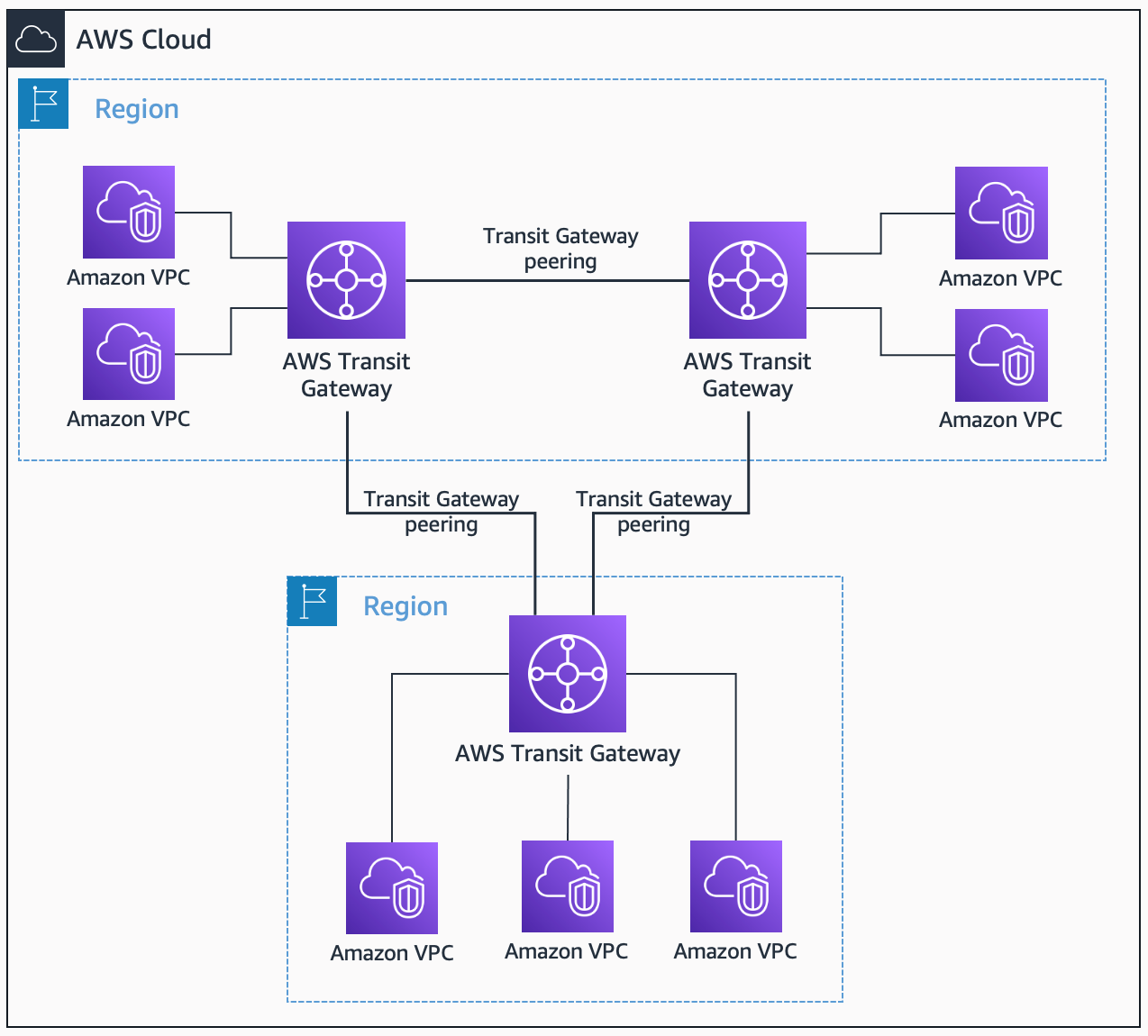
Implementing VPC Peering
VPC peering allows two VPCs to communicate with each other as if they were within the same network. This feature is particularly useful for securely connect remote IoT VPC on AWS, as it enables seamless communication between IoT devices and other resources within the network.
To implement VPC peering, follow these steps:
- Create a VPC peering connection between the source and destination VPCs.
- Update route tables to allow traffic to flow between the two VPCs.
- Test the connection to ensure that communication is functioning as expected.
By leveraging VPC peering, organizations can enhance connectivity and ensure secure communication between IoT devices and other resources within the network.
Data Encryption Strategies
Data encryption is a critical component of IoT security, ensuring that sensitive information remains protected throughout the network. Below are some effective strategies for encrypting data in an AWS VPC environment:
1. Client-Side Encryption
Encrypt data on the client side before transmitting it to the cloud, ensuring that sensitive information remains secure even if intercepted during transmission.
2. Server-Side Encryption
Use server-side encryption to protect data stored in AWS services, such as S3 and RDS. This method ensures that data remains encrypted at rest, providing an additional layer of security.
3. Key Management
Implement a robust key management strategy to protect encryption keys and ensure that only authorized personnel can access them. AWS Key Management Service (KMS) provides a secure and scalable solution for managing encryption keys.
Monitoring and Logging
Continuous monitoring and logging are essential for detecting and responding to security threats in real-time. Below are some strategies for effectively monitoring and logging IoT devices within AWS VPC:
- CloudWatch: Use Amazon CloudWatch to monitor metrics and log data from IoT devices, enabling quick detection and response to potential issues.
- GuardDuty: Leverage AWS GuardDuty to detect and respond to malicious activity and unauthorized behavior within the network.
- Config: Implement AWS Config to track changes to resources and ensure compliance with security policies.
By implementing these monitoring and logging strategies, organizations can proactively address security threats and maintain the integrity of their IoT ecosystems.
Conclusion and Next Steps
Securing IoT devices within AWS VPC requires a comprehensive approach that addresses the unique challenges of this rapidly evolving field. By following the strategies and best practices outlined in this article, organizations can securely connect remote IoT VPC on AWS and protect their data and infrastructure from potential threats.
To further enhance your IoT security, consider exploring additional AWS services and resources, such as AWS IoT Device Defender and AWS Security Hub. These tools provide advanced capabilities for monitoring, analyzing, and responding to security threats, ensuring the safe operation of your IoT devices.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and AWS services. Together, we can build a safer and more secure digital future for everyone.